Librespace, who are the people behind the open hardware/source SatNOGS satellite ground station project have recently released a comprehensive paper (pdf) that compares multiple software defined radios available on the market in a realistic laboratory based signal environment. The testing was performed by Alexandru Csete (@csete) who is the programmer behind GQRX and Gpredict and Sheila Christiansen (@astro_sheila) who is a Space Systems Engineer at Alexandru's company AC Satcom. Their goal was to evaluate multiple SDRs for use in SatNOGS ground stations and other satellite receiving applications.
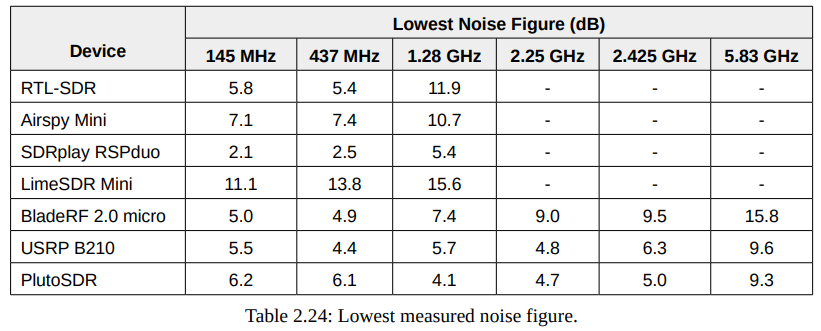
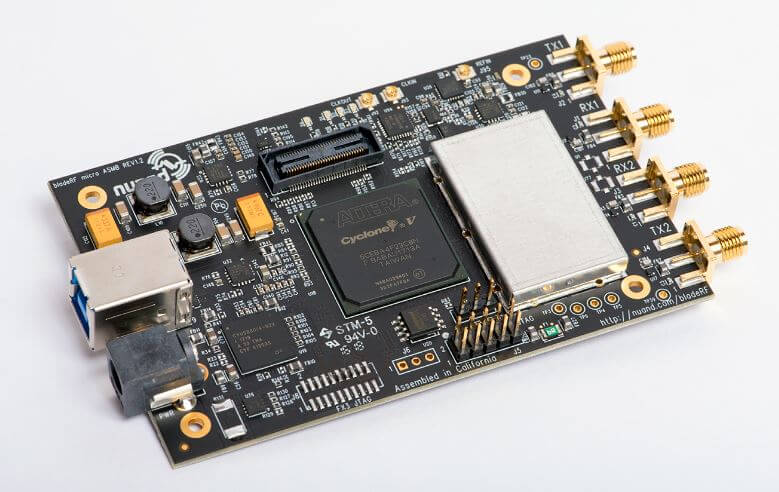
The SDRs tested include the RTL-SDR Blog V3, Airspy Mini, SDRplay RSPduo, LimeSDR Mini, BladeRF 2.0 Micro, Ettus USRP B210 and the PlutoSDR. In their tests they measure the noise figure, dynamic range, RX/TX spectral purity, TX power output and transmitter modulation error ratio of each SDR in various satellite bands from VHF to C-band.
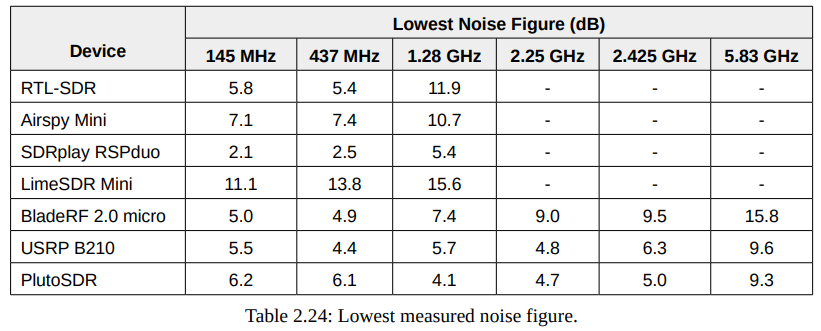
The paper is an excellent read, however the results are summarized below. In terms of noise figure, the SDRplay RSPduo with it's built in LNA performed the best, with all other SDRs apart from the LimeSDR being similar. The LimeSDR had the worst noise figure by a large margin.
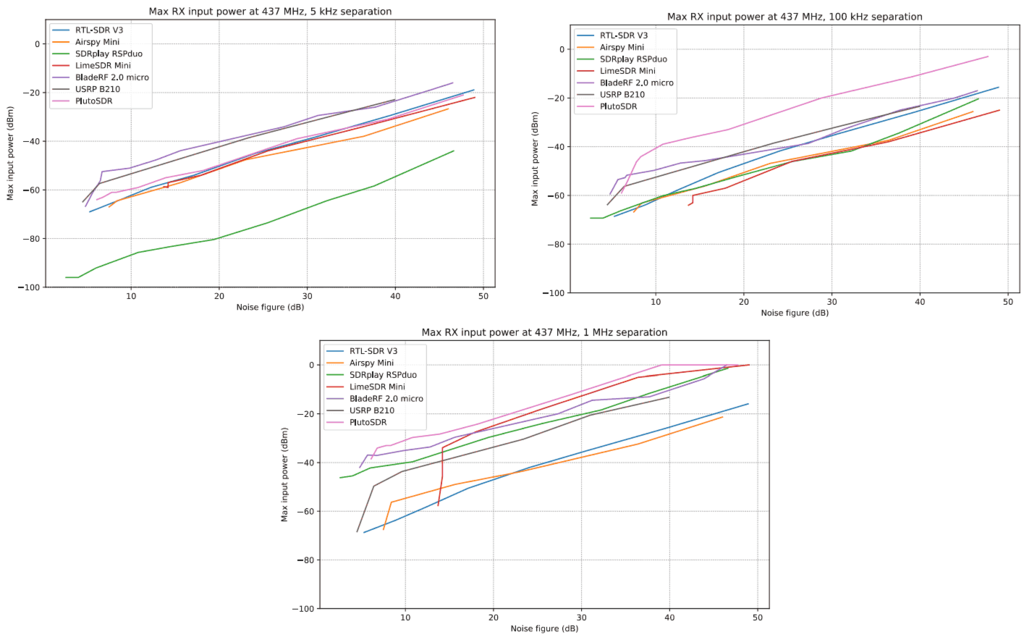
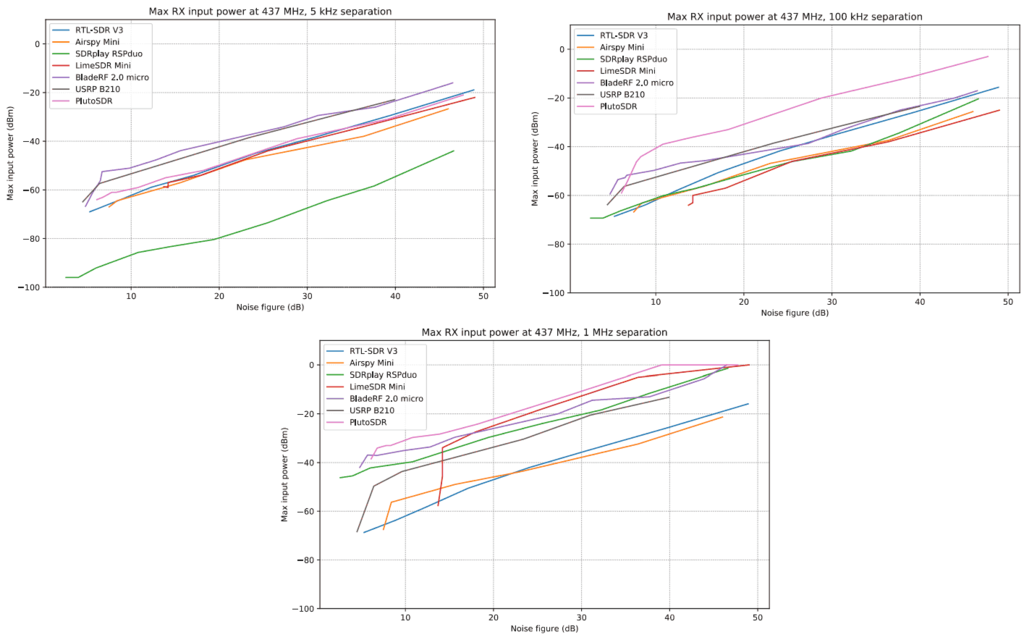
In terms of dynamic range, the graphs below show the maximum input power of a blocking signal that the receivers can tolerate vs. different noise figures at 437 MHz. They write that this gives a good indication of which devices have the highest dynamic range at any given noise figure. The results show that when the blocking signal is at the smallest 5 kHz spacing the RSPduo has poorest dynamic range by a significant margin, but improves significantly at the 100 kHz and 1 MHz spacings. The other SDRs all varied in performance between the different blocking signal separation spacings.
Overall the PlutoSDR seems to perform quite well, with the LimeSDR performing rather poorly in most tests among other problems like the NF being sensitive to touching the enclosure, and the matching network suspected as being broken on both their test units. The owner of Airspy noted that performance may look poor in these tests as the testers used non-optimized Linux drivers, instead of the optimized Windows drivers and software, so there is no oversampling, HDR or IF Filtering enabled. The RSPduo performs very well in most tests, but very poorly in the 5 kHz spacing test.
 The rest of the paper covers the TX parameters, and we highly recommend going through and comparing the individual result graphs from each SDR test if you want more information and results from tests at different frequencies. The code and recorded data can also be found on the projects Gitlab page at https://gitlab.com/librespacefoundation/sdrmakerspace/sdreval.
The rest of the paper covers the TX parameters, and we highly recommend going through and comparing the individual result graphs from each SDR test if you want more information and results from tests at different frequencies. The code and recorded data can also be found on the projects Gitlab page at https://gitlab.com/librespacefoundation/sdrmakerspace/sdreval.